An 18-year-old flaw in the NGINX open-source web server, discovered using an autonomous scanning system, can be exploited for denial of service and, under certain conditions, remote code execution.
The vulnerability is tracked as CVE-2026-42945 and received a critical severity rating of 9.2, based on the latest version of the Common Vulnerability Scoring System (CVSS).
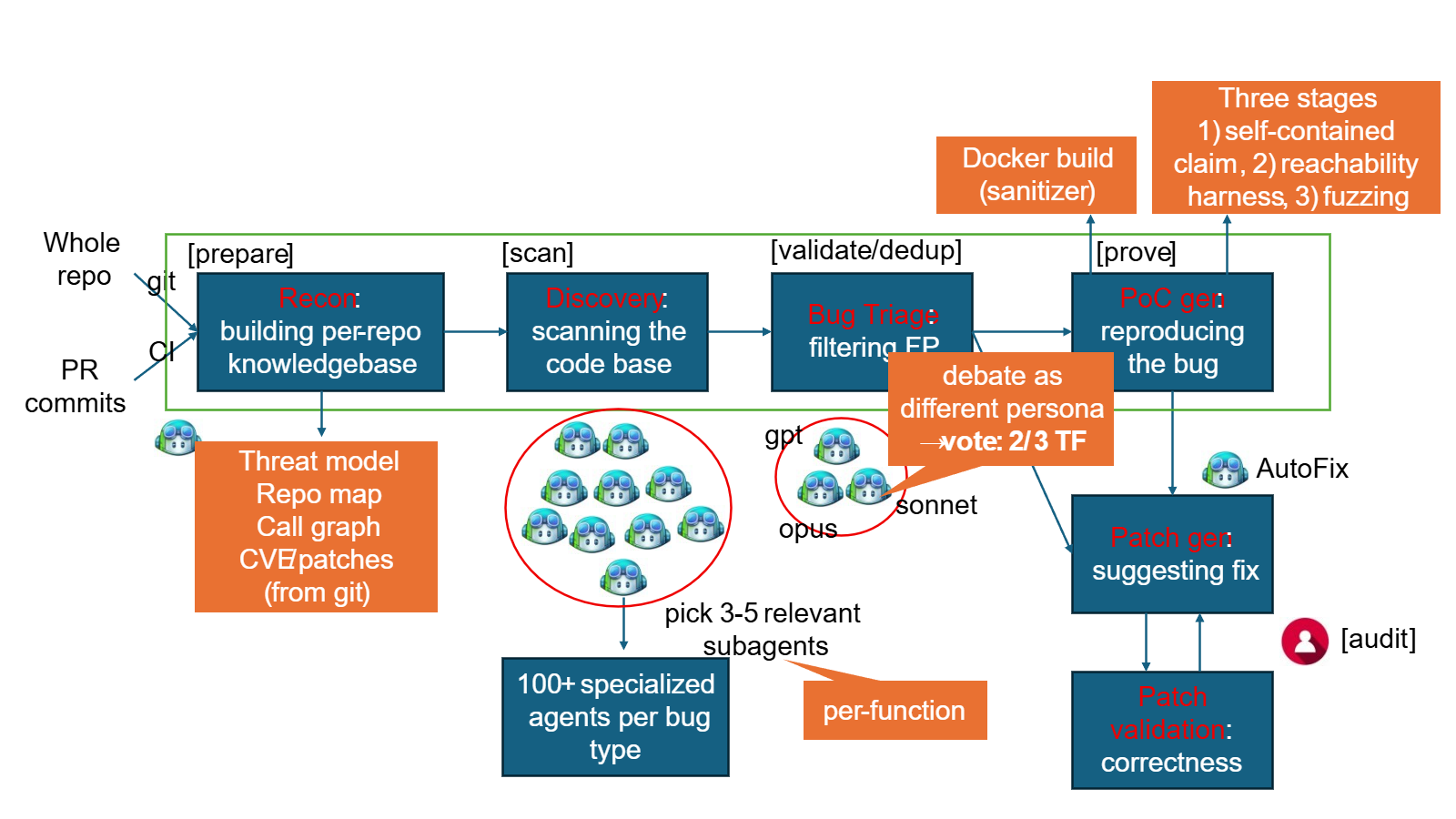
Three more memory corruption security issues were discovered in the same six-hour code scanning session by researchers at AI-native security company DepthFirst AI.
NGINX is a massively used web server and reverse proxy platform, powering a third of the top ranked websites. It can efficiently balance load by distributing incoming network traffic to multiple backend servers and reduce load times by caching content.
Owned and maintained by American tech firm F5, the web server is used by cloud providers, SaaS companies, banks, media platforms, e-commerce sites, and in Kubernetes clusters.