by Duncan Riley
Microsoft Corp. today detailed a new artificial intelligence-powered vulnerability discovery system that uncovered 16 previously unknown flaws in Windows networking and authentication components, including four critical remote code execution bugs patched in this month’s Patch Tuesday release.
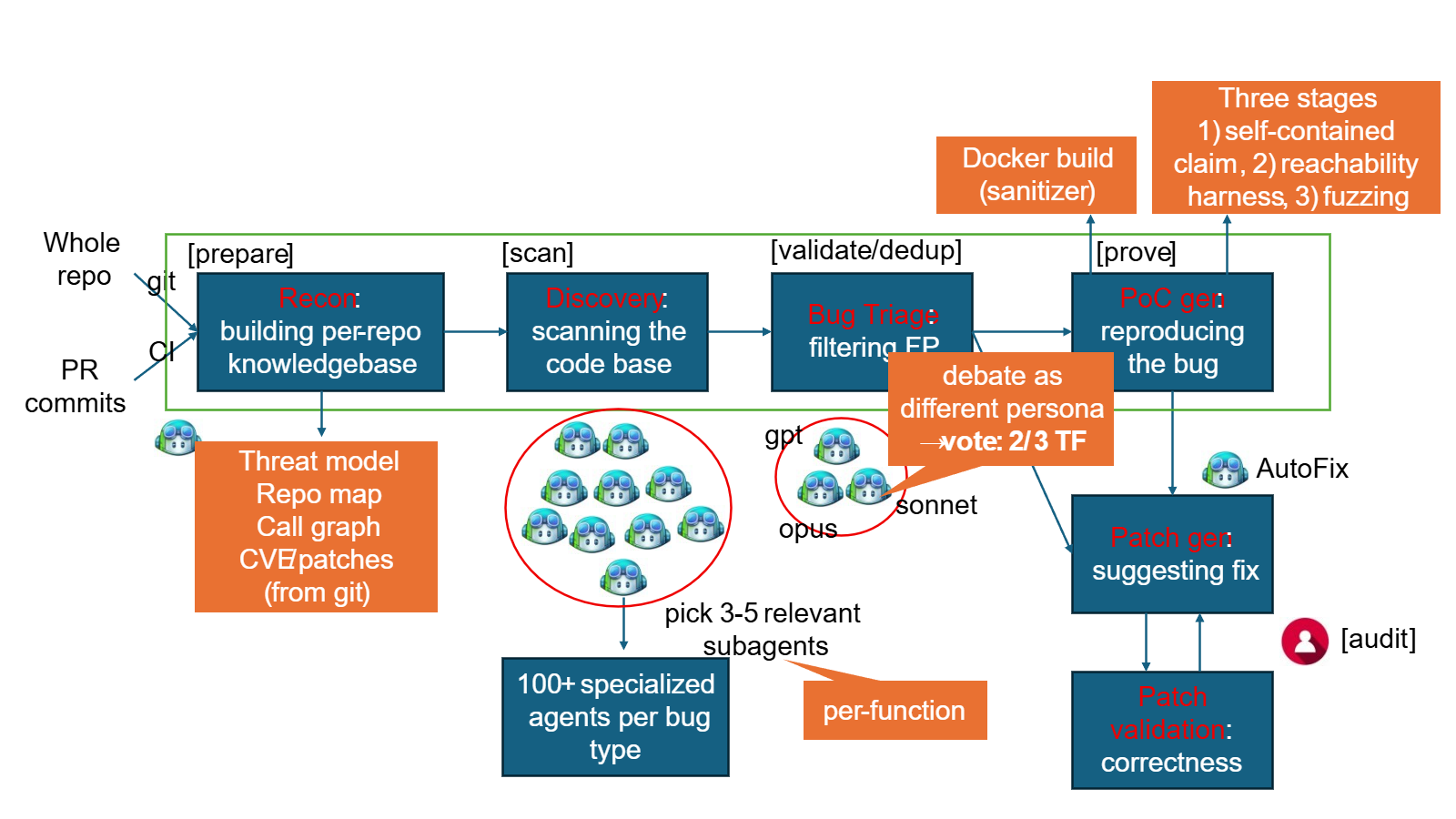
The system, codenamed MDASH for multi-model agentic scanning harness, was built by Microsoft’s Autonomous Code Security team in collaboration with the company’s Windows Attack Research and Protection group. MDASH orchestrates more than 100 specialized AI agents across an ensemble of frontier and distilled models to find, debate and prove exploitable bugs from end to end.
The 16 vulnerabilities span the Windows TCP/IP stack, the IKEEXT IPsec service, HTTP.sys, Netlogon, DNS resolution and the Telnet client.
Ten of the vulnerabilities were kernel-mode and six were usermode and most were reachable from a network position without credentials.