ByDavey Winder,
Senior Contributor.
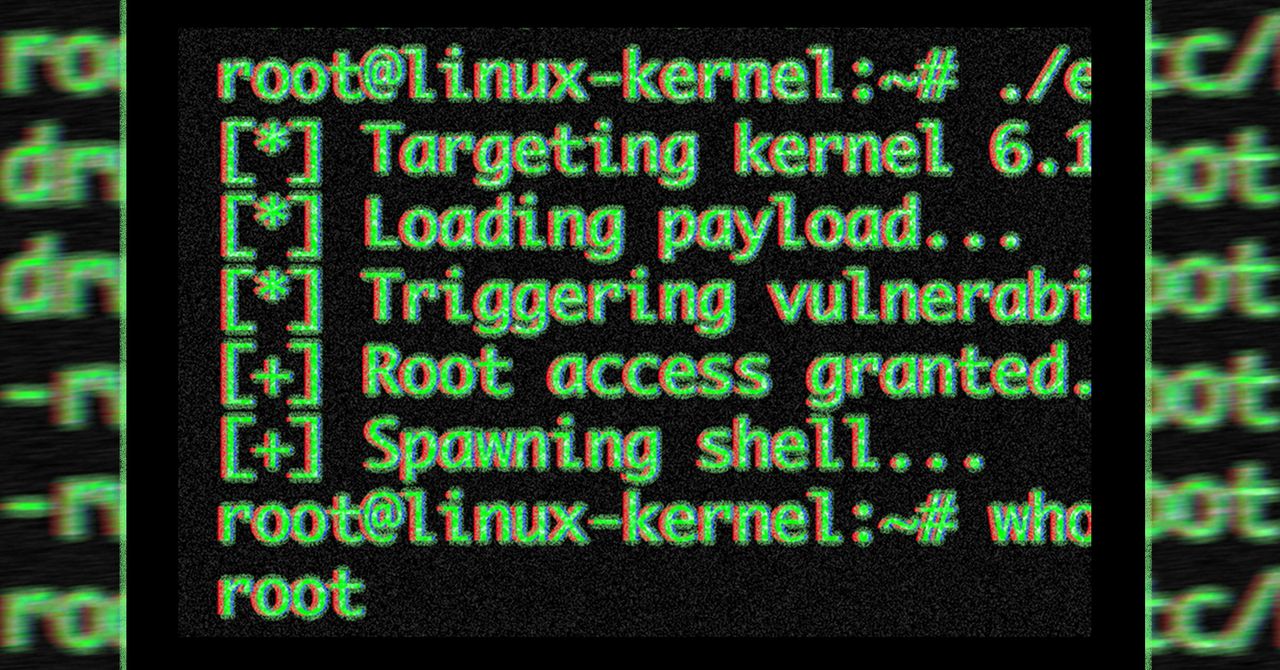
Updated May 10: This article regarding the critical Dirty Frag Linux kernel zero-day vulnerability that gives attackers root access with no patch available has been updated to include comments from security experts at Black Duck, Bugcrowd and Sectigo.
If you thought that Linux was somehow the safe and secure choice of operating system, you might want to think again. Hot on the heels of the Copy Fail access vulnerability that had remained hidden for 9 years comes news that a new zero-day, with no patch available and granting hackers root, has been confirmed. On Friday, May 8, 2026, the Dirty Frag vulnerability was publicly disclosed after a strict embargo tregarding the vulnerability was broken. As such, and with a proof of concept exploit known, it’s now only a matter of time before threat actors use this in the wild to attack systems. Here’s what we know about CVE-2026-43284 and the workaround you can employ to mitigate against attacks.
Why is it always a Friday? Just as security teams and end users alike look forward to the weekend, a security issue rears its ugly head, putting a stop to all that. With the major Linux distributions still rolling out patches for the Copy Fail vulnerability, which the U.S. Cybersecurity and Infrastructure Security Agency has confirmed is now being exploited by attackers, comes news that an even worse issue is out there. Dirty Frag, officially now tracked by the Common Vulnerabilities and Exposures database as CVE-2026-43284, has been confirmed and publicly disclosed, all before a patch is ready to roll.