Microsoft has built an agentic multi-model system that uses more than 100 specialized AI agents to detect software vulnerabilities.
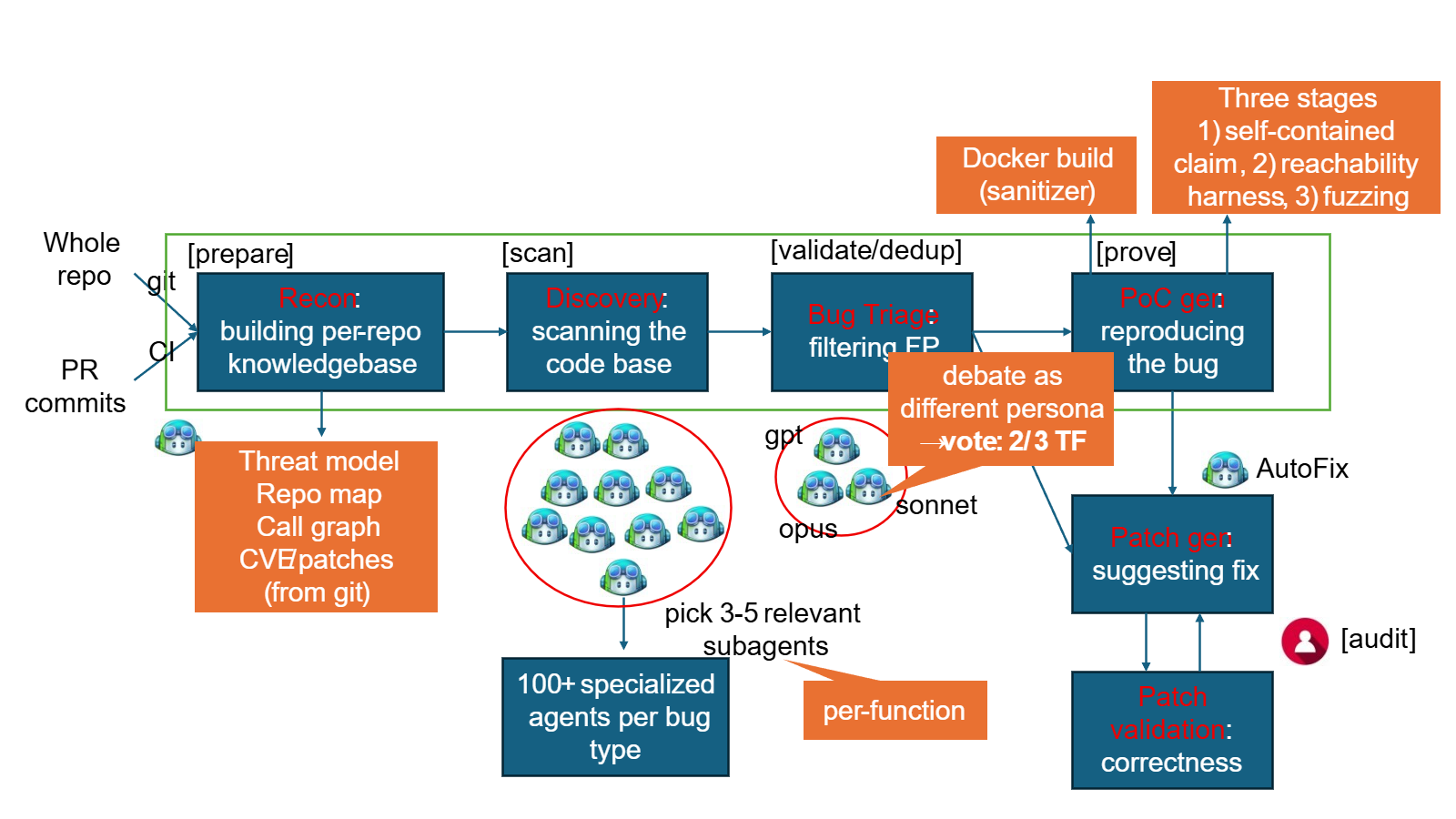
The security system, called MDASH (Multi-Model Agentic Scanning Harness), is designed to automatically find security vulnerabilities in software. Unlike approaches that rely on a single AI model like Claude Mythos, MDASH orchestrates more than 100 specialized AI agents across an ensemble of frontier and distilled models, according to Microsoft.
On Patch Tuesday, May 12, 2026, Microsoft reported 16 new vulnerabilities (CVEs) in the Windows networking and authentication stack that MDASH discovered. The company classifies four of these as critical, including remote code execution vulnerabilities in the tcpip.sys kernel component, the IKEv2 service (ikeext.dll), netlogon.dll, and dnsapi.dll.
Ten of the 16 vulnerabilities affect kernel mode, and most are accessible from the network without authentication, Microsoft says. The company points out that its own code base is especially hard to audit: Windows, Hyper-V, and Azure are proprietary and aren't part of public training data.
The system works in a four-stage pipeline. First, it analyzes the source code and maps the attack surface. Specialized auditor agents then scan the code for suspicious areas. In the third stage, a second group of agents, which Microsoft calls "debaters," argue for and against the exploitability of each finding. Duplicates are then merged before Evidence Leader agents attempt to trigger the vulnerability through specific inputs in the final stage.