Turla Turns Kazuar Backdoor Into Modular P2P Botnet for Persistent Access
Turla turns Kazuar into a 3-module P2P botnet, enabling stealthy C2, resilient tasking, and persistent access.
38articoli totali nell'archivio
Turla turns Kazuar into a 3-module P2P botnet, enabling stealthy C2, resilient tasking, and persistent access.
Claw Chain flaws in OpenClaw 2026.4.22 enable data theft, privilege escalation, and persistence when chained.

Trusted-tool abuse hit 84% of 700,000 incidents, driving 45-day assessments that reduce attack surface by 30%+.

CVE-2026-42897 is exploited in on-prem Exchange; crafted emails enable spoofing, forcing urgent mitigation.
CISA added CVE-2026-20182, a CVSS 10.0 Cisco Catalyst SD-WAN Controller authentication bypass flaw, to its KEV catalog.

CVE-2026-20182 bypasses Cisco SD-WAN auth via DTLS port 12346, enabling admin access after May 2026 exploitation.
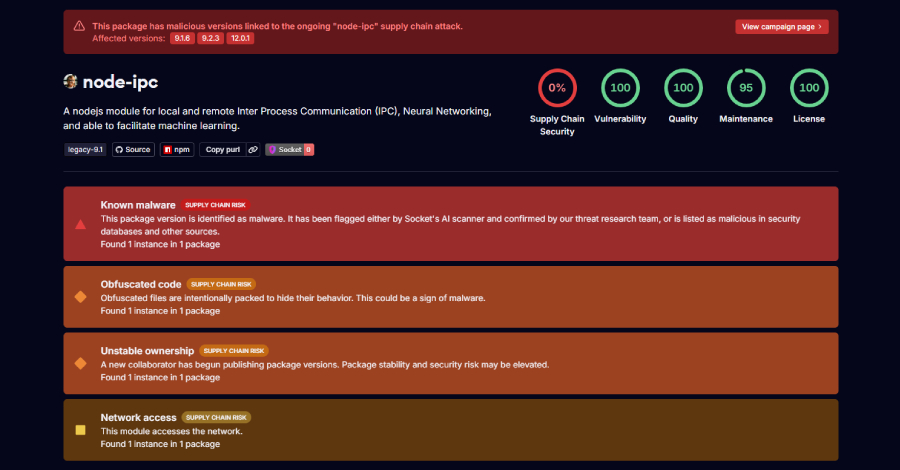
Three node-ipc versions contain stealer/backdoor code, exposing developer and cloud secrets to exfiltration.

Weekly ThreatsDay Bulletin: supply chain attacks, fake support lures, AI tampering, data leaks, ransomware, and exploited flaws.
PraisonAI auth bypass exposed /agents after May 11 disclosure, enabling exploit checks within 3h44m.

AI hallucinations are confident but false outputs that pose major security risks. Learn how they impact threat detection and how…
YellowKey bypasses BitLocker via WinRE USB FsTx files, exposing Windows 11 and Server 2022/2025 systems.
Fragnesia CVE-2026-46300 corrupts Linux page cache via XFRM ESP-in-TCP, enabling local root access on major distros.
NGINX Rift CVE-2026-42945 scores 9.2 after 18 years, enabling unauthenticated RCE or DoS via crafted HTTP requests.

Microsoft’s new MDASH AI system found 16 Windows vulnerabilities fixed in this month’s Patch Tuesday, including 2 RCE flaws in…
FamousSparrow reused ProxyNotShell from Dec 2025-Feb 2026, deploying Deed RAT and TernDoor to sustain energy-sector access.
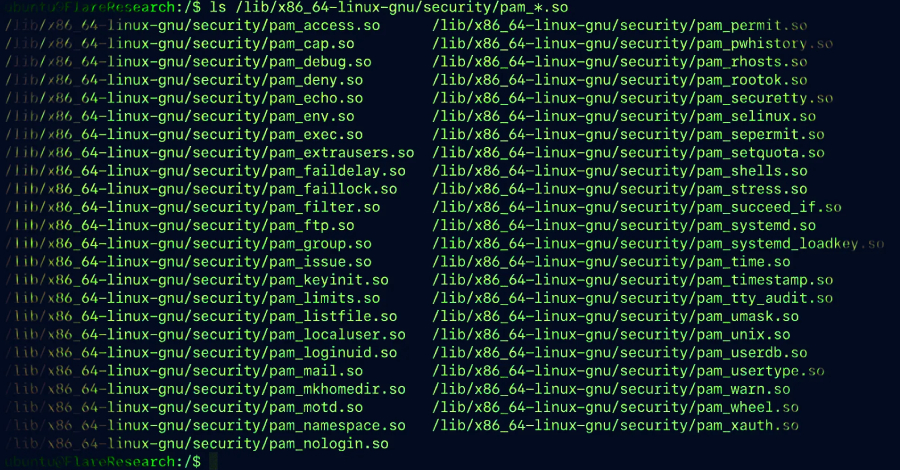
PamDOORa Linux backdoor abuses PAM modules for SSH persistence and credential theft, increasing Linux server compromise risks.
Dirty Frag exposes Linux systems to root escalation through chained kernel flaws, impacting Ubuntu, RHEL, Fedora, and others.

CVE-2026-0300 exploited after April 9 attempts enables PAN-OS RCE, leading to stealth espionage and lateral movement by April 29.

ThreatsDay Bulletin: fake apps, supply chain attacks, AI-fueled exploits, ransomware chaos, and the biggest cyber threats this…

Delayed IR access and 14-day logs limit visibility during breaches, increasing attacker dwell time and recovery costs.

CyberStars Awards 2026 launched as a global program recognizing cybersecurity excellence across products, companies, and…

CVE-2026-0300 exploited via public PAN-OS portal before May 13, 2026 patch, enabling root RCE on firewalls.
Apache fixes CVE-2026-23918 in HTTP/2; double-free flaw enables DoS and RCE, impacting version 2.4.66 users.

AI infrastructure exposes 1M services from 2M hosts due to weak defaults, increasing risk of data leaks and system compromise
Microsoft disclosed a credential theft campaign targeting 35,000+ users at 13,000+ organizations across 26 countries.

MOVEit Automation flaws (CVE-2026-4670, CVE-2026-5174) enable bypass and escalation, risking enterprise data exposure.




84% of attacks misuse legitimate tools across 700,000 incidents, reducing detection effectiveness and increasing internal breach…

Trellix reports source code breach with partial repository access, no exploitation found, raising security concerns.
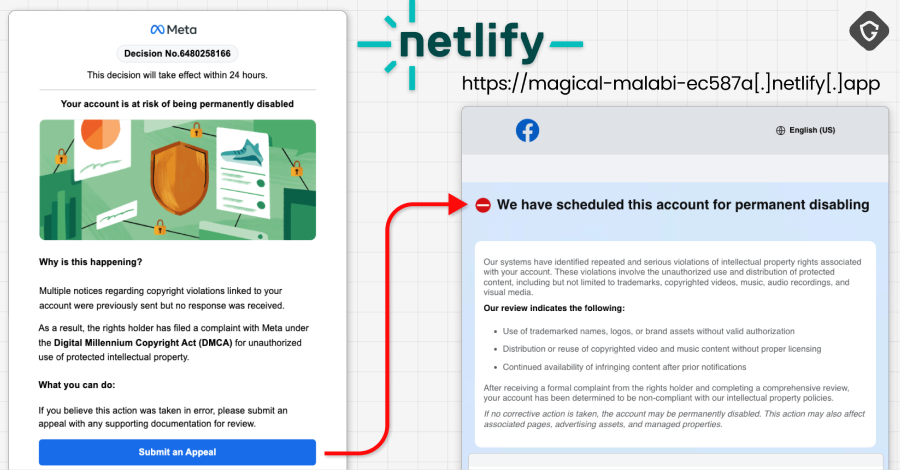
30,000 Facebook accounts hacked via AppSheet phishing emails, exploiting Meta lures, leading to large-scale account theft and…

11,000+ malicious domains fuel GovTrap impersonation campaign, exploiting global government trust to steal data and payments.