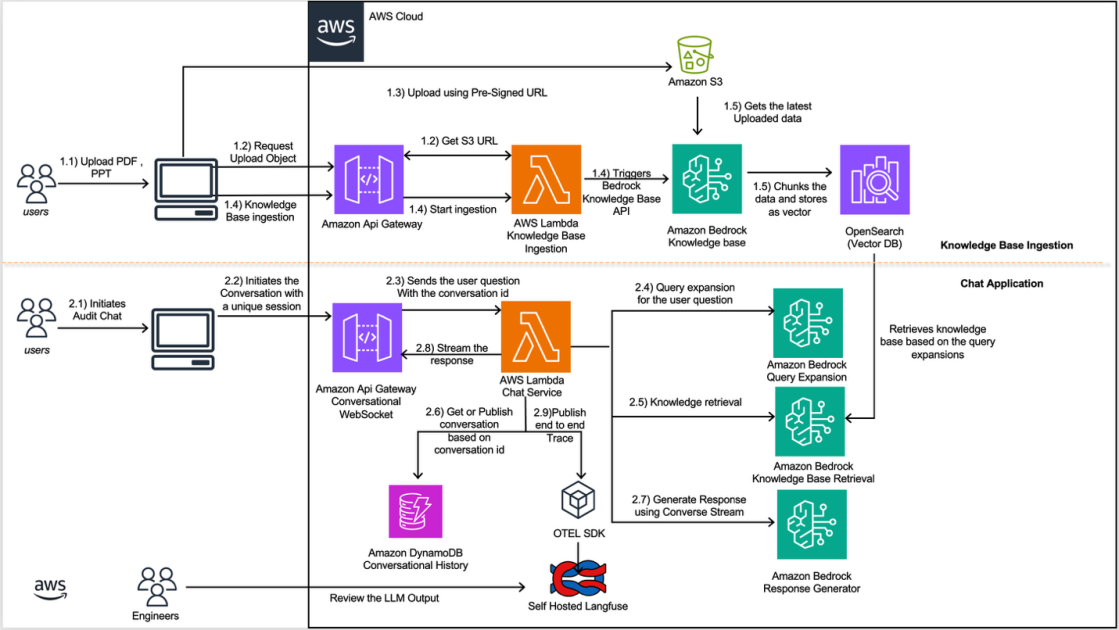
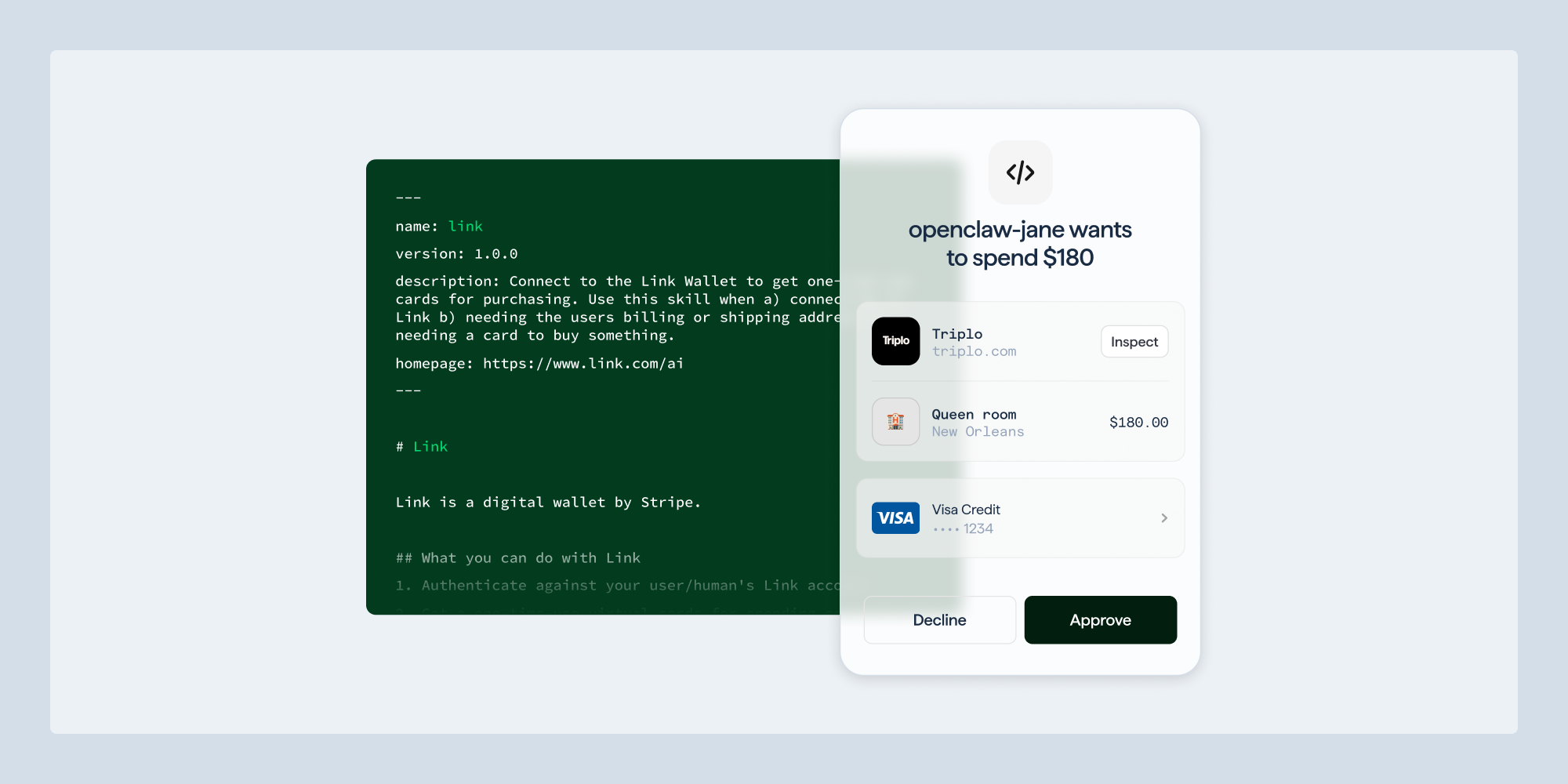
DollarsPixabayTwo announcements in a single week pushed enterprise AI agents past a line that boardrooms have not yet drawn. On May 7, AWS previewed Amazon Bedrock AgentCore Payments, a managed capability built with Coinbase and Stripe that lets agents autonomously pay for APIs, MCP servers, web content, and other agents up to a session-level spending limit. One week later, on May 14, a leaked onboarding screen for Google's upcoming Gemini Spark agent told testers the agent "may do things like share your info or make purchases without asking." Gemini Spark is widely expected to be a centerpiece of Google I/O on May 19.The same seven-day window moved AI agents from systems that recommend purchases to systems that complete them. The infrastructure to spend money is now a checkbox in Amazon Bedrock and a default behavior in the next iteration of Gemini. The governance, audit, and insurance frameworks enterprises rely on were written for a world where a human approved every transaction.What AWS Actually ShippedAmazon Bedrock AgentCore Payments routes transactions through the x402 protocol, an open HTTP-native standard that turns the long-dormant HTTP 402 "Payment Required" status code into a machine-to-machine payment rail. When an agent hits a paid endpoint, AgentCore handles wallet authentication, stablecoin settlement on Base, and proof delivery without breaking the agent's reasoning loop. Developers connect either a Coinbase CDP wallet or a Stripe Privy wallet, fund it through stablecoins or a debit card, and set a per-session spending cap. The preview runs in four AWS regions and integrates the Coinbase x402 Bazaar MCP server, which exposes more than 10,000 paid endpoints agents can search and pay for without prior configuration.Warner Bros. Discovery is testing AgentCore Payments for premium content access including live sports, and Heurist AI is building a research agent that performs financial analysis for end users. AWS has stated that broader commerce flows including hotel bookings, travel reservations, and merchant payments are next.Gemini Spark is a different shape. According to onboarding text decompiled from Google app beta version 17.23, Spark draws from connected apps, browsing sessions, scheduled tasks, location data, and a feature Google calls Personal Intelligence to run inbox cleanup, meeting briefings, and online tasks in the background. The disclosure that the agent may make purchases without asking is positioned as a feature of the experimental tier.MORE FOR YOUAnthropic's Claude Cowork sits on the other end of the spectrum and blocks autonomous purchases at the policy level. Three of the four major frontier AI vendors are now shipping agents that can move money. The fourth has positioned that boundary as a feature.The Governance Gap CXOs Have Not SizedThe questions boards have not yet asked include who is liable when an agent makes a purchase the user did not approve, what happens to know your customer and anti money laundering controls when the buying party is software, how procurement policies should treat agent driven spend, and whether existing SOC 2 Type II and ISO 27001 attestations cover any of this.The legal frame is moving faster than the audit frame. California's AB 316, which took effect January 1, 2026, prevents defendants from citing an AI system's autonomous operation as a defense to liability claims. The "AI did it" argument is foreclosed in California. Colorado's AI Act, effective June 2026, will require deployers of high-risk AI systems to run annual impact assessments. The EU AI Act's general-purpose model rules already apply, and broader consumer-facing transparency obligations kick in on August 2, 2026.SOC 2 was not designed for actors that act without a human request. Auditors typically treat unattributable privileged actions as accountability gaps, because the framework expects sensitive operations to trace back to an accountable individual rather than an autonomous system. An agent that initiates a payment based on a tool result, a prompt injection, or a poisoned web page does not produce the audit artifact the framework was built around. The same gap shows up in cyber insurance, where carriers have started adding AI supplements to renewal applications and asking for governance evidence that most SOC 2 reports do not contain.The Failure Modes Are KnowableThe session-level spending cap is the primary protection AWS markets for AgentCore Payments. It is real, and it is also the same shape of control that bounded carding fraud in 2008. A per-transaction limit constrains the worst single event without constraining the aggregate vector. An agent that encounters a paid endpoint controlled by an attacker, reads a poisoned instruction telling it to "verify" a wallet through 200 sub-cent calls, and stays inside the per-session cap on every call can still drain the wallet in aggregate.Prompt injection is the underlying risk. Anthropic has reported roughly a 1 percent success rate against its internal Claude Cowork testing, the best public number from any frontier vendor. The residual 1 percent now operates at machine speed against an agent with wallet access. The failure mode that mattered in early 2026 was data exfiltration. The failure mode that matters from May 2026 forward is funds movement.What Boards Should Actually Do Before The Next AuditThe first practical step is to map agent identities the way enterprises already map human and service identities. Non-human identities are projected to exceed 45 billion by the end of 2026 according to research cited in NIST's draft framework, more than twelve times the human global workforce, while only about 10 percent of organizations report having a strategy to manage them. Every agent that can move money belongs in the same identity inventory as every human who can.The second step is to write procurement and accounts payable policies that recognize software as a buying party. Existing policies assume a human initiator, a documented purchase order, and an attributable approval chain. A research agent that buys a market data feed through a stablecoin micropayment at runtime fits none of those patterns. The control gap will close either through policy or through the first public incident, and policy is cheaper.The third step is to reread the SOC 2 and ISO 27001 attestations from vendors whose agents will sit inside the enterprise perimeter with payment authority. The relevant question is not whether the vendor carries the certifications. It is whether the audit period covered agent driven transactions and whether the control language addressed actions taken without a human in the loop.Vendors are framing agent payments as a productivity unlock. The CXO frame is narrower. This is the week AI moved from advice to action with financial consequences, and audit, governance, and insurance markets have not caught up.
Agent Payments Arrive Before Audit And Insurance Catch Up
AWS launched agent payments on May 7 and Gemini Spark leaked a week later. CXOs now face a governance gap that SOC 2, ISO 27001, and cyber insurance never anticipated.