TL;DRFour chainable OpenClaw flaws dubbed “Claw Chain” let attackers weaponise the agent’s own sandbox. Patches are live.
Cybersecurity researchers at Cyera have disclosed four vulnerabilities in OpenClaw that, when chained together, allow an attacker to steal sensitive data, escalate privileges, and establish persistent control over a compromised host. The flaws, collectively dubbed “Claw Chain,” affect OpenClaw’s OpenShell managed sandbox backend and its MCP loopback runtime. All four have been patched in OpenClaw version 2026.4.22.
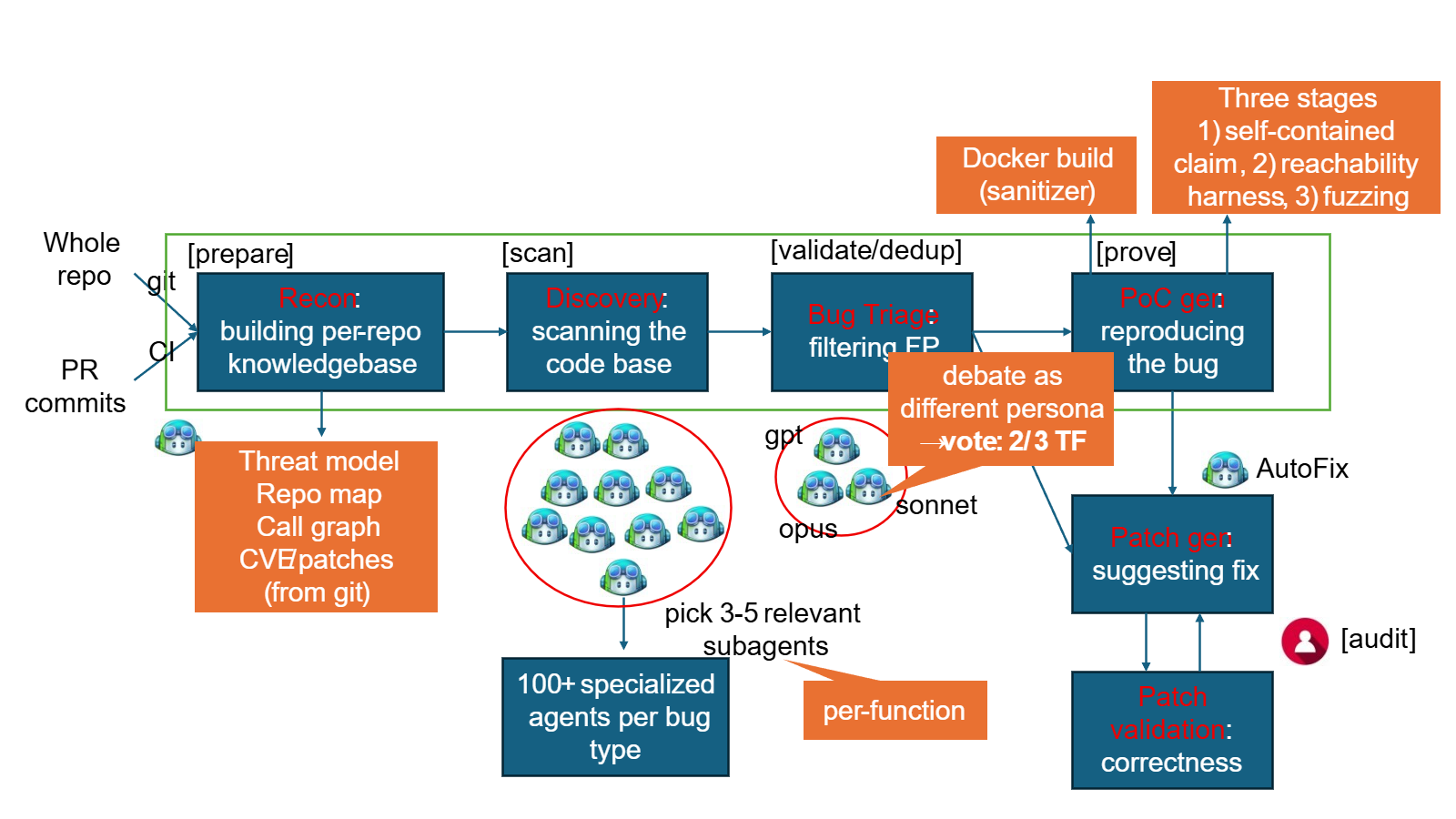
The attack chain works in four stages. First, a malicious plugin, prompt injection, or compromised external input gains code execution inside the OpenShell sandbox. Second, two of the vulnerabilities, CVE-2026-44113 and CVE-2026-44115, are exploited to expose credentials, secrets, and sensitive files. Third, CVE-2026-44118 is used to obtain owner-level control of the agent runtime by exploiting an improperly validated ownership flag. Fourth, CVE-2026-44112, the most severe of the four with a CVSS score of 9.6, is used to plant backdoors, modify configuration, and establish persistence outside the sandbox.
The most architecturally interesting flaw is CVE-2026-44118, which stems from OpenClaw trusting a client-controlled flag called senderIsOwner without validating it against the authenticated session. Any non-owner loopback client could impersonate an owner and gain control over gateway configuration, cron scheduling, and execution environment management. The fix, according to OpenClaw’s advisory, involves issuing separate owner and non-owner bearer tokens, with senderIsOwner now derived exclusively from the authenticating token rather than from a spoofable header.