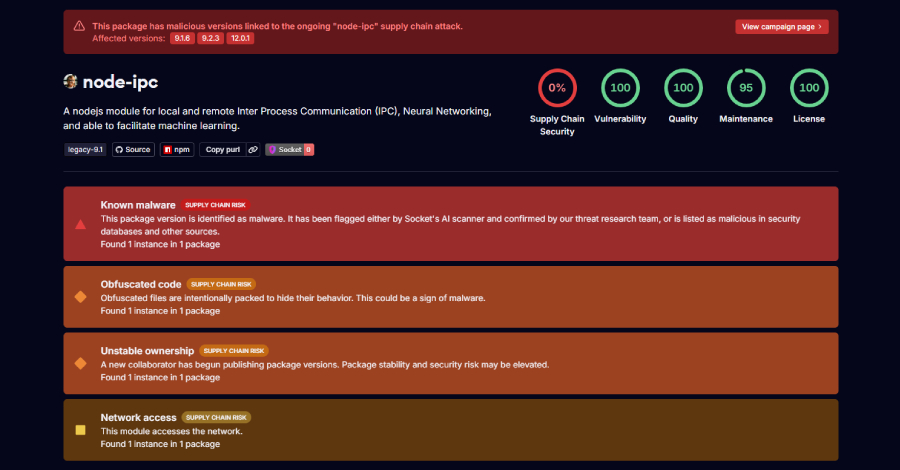
In recent months, a new infostealer malware known as REMUS has emerged across the cybercrime landscape, drawing attention from security researchers and malware analysts. Several technical analyses published in recent months focused on the malware’s capabilities, infrastructure, and similarities to Lumma Stealer, including browser targeting mechanisms, and credential theft functionality and more.
However, far less attention has been given to the underground operation behind the malware itself.
An analysis conducted by Flare researchers of 128 posts linked to the REMUS underground operation between February 12 and May 8, 2026, provides a rare look into how the group presents, develops, and operationalizes the malware within underground communities. By analyzing the actor’s advertisements, update logs, feature announcements, operational discussions, and customer-facing communications, the research helps map how the operation evolved over time and what priorities drove its development.
The findings reveal not only the rapid evolution of the stealer’s capabilities, but also a growing focus on commercialization, operational scalability, session theft, and password-manager targeting. More broadly, the activity offers insight into how modern malware-as-a-service (MaaS) operations increasingly resemble structured software businesses, with continuous development cycles, operational refinements, and features designed to improve usability, persistence, and long-term monetization.