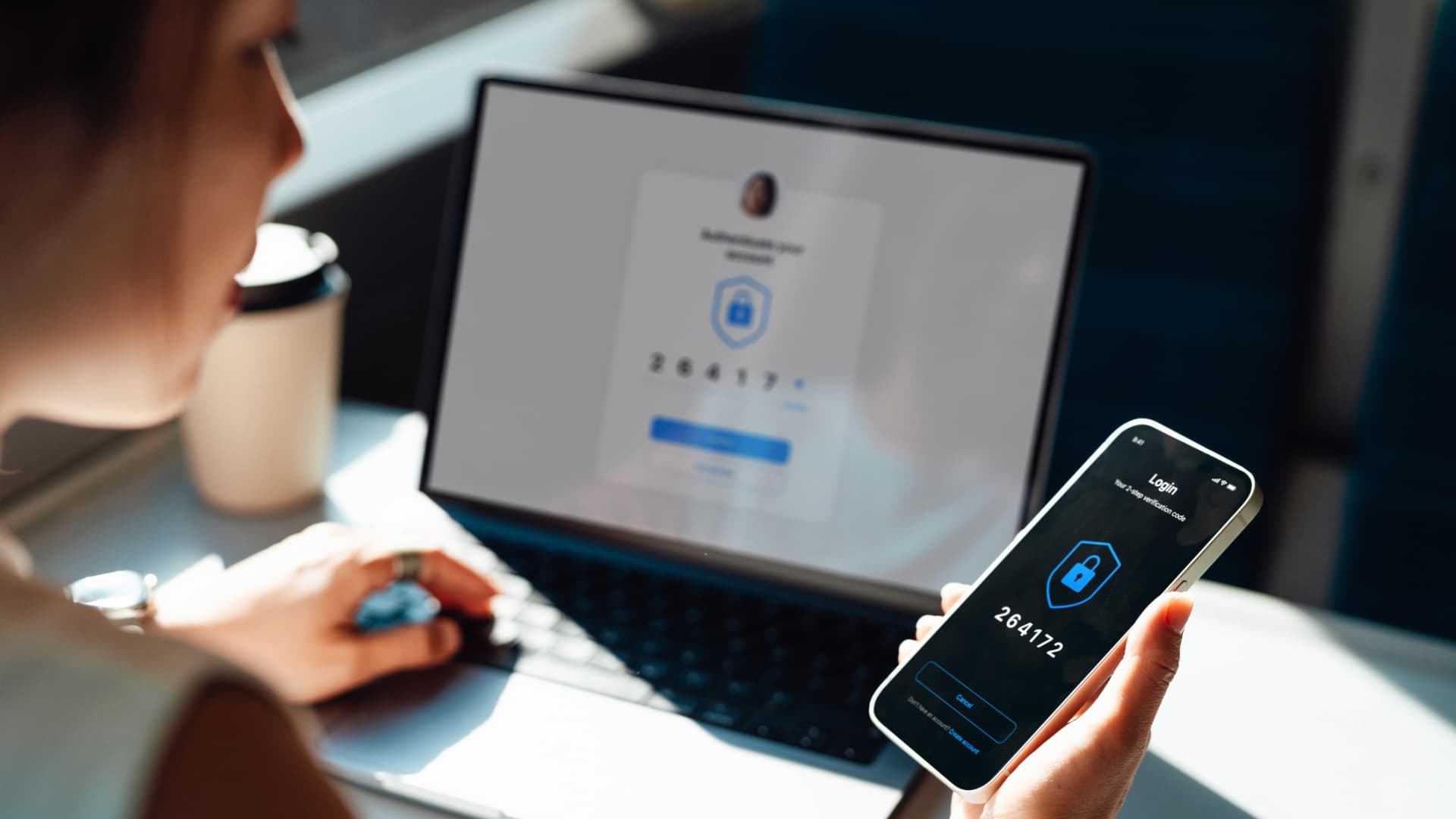
For the past 20 years, multi-factor authentication (MFA) has been regarded as the gold standard for replacing passwords to achieve strong authentication. While one-time passcodes (OTPs), hardware tokens, and push notifications have enhanced protection against identity-based attacks, MFA no longer offers ironclad security.
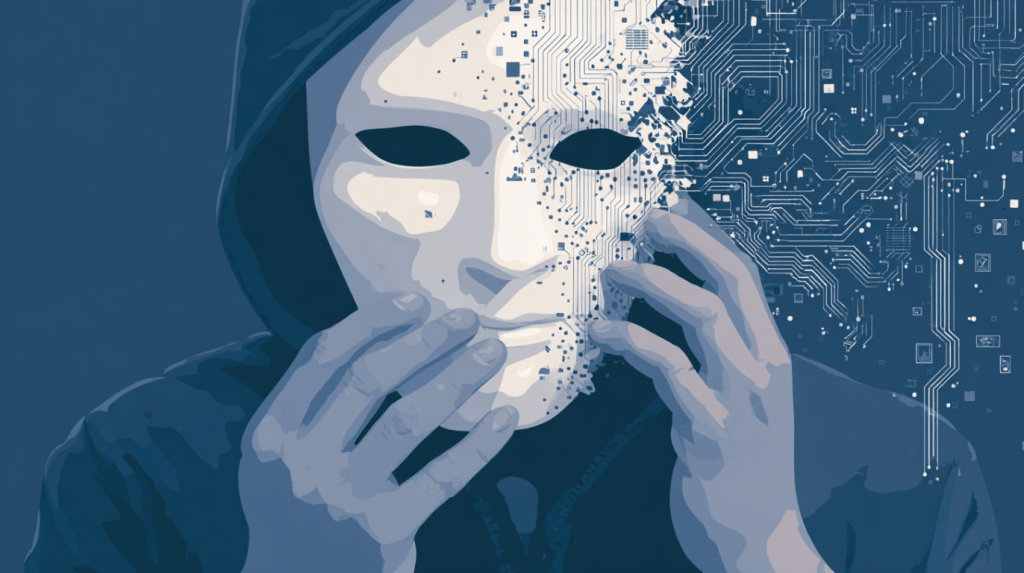
Phishing, social engineering, and man-in-the-middle attacks continue to bypass MFA. Meanwhile, users face an increasingly frustrating authentication experience. Clearly, MFA is past its prime. Several factors have contributed to the downfall of MFA.
First, many MFA implementations, such as SMS OTPs and email codes, are vulnerable to interception. Attackers exploit SIM-swapping techniques or adversary-in-the-middle (AitM) attacks to steal authentication credentials. Even push notifications have become targets through MFA fatigue attacks, where users unknowingly approve fraudulent login attempts.
Second, hardware-based authentication methods like YubiKeys offer strong protection against phishing but present usability challenges. Users often misplace their devices, distribution requires logistical coordination, and IT support demands increase when employees work remotely or across multiple devices. Although federated identity solutions ease access through single sign-on (SSO), they still depend on central authorities, creating potential points of failure and raising privacy concerns when third parties manage authentication.