Fonte
theregister.com
281articoli totali nell'archivio

AWS to Quick admins: The access control didn't work, but you weren't using it…
If a setting fails in the forest and nobody hears it ...

Google's AI-enabled mouse pointer understands 'this' and 'that'
Right-clicking could go the way of the 3.5-inch floppy at the Chocolate Factory


Anthropic butts in to small business, promises help with payroll and other core…
But Pro or Max biz users should know that the company may train its AI on your data
Bug hunter tracks down three massive MCP flaws and one vendor won't fix theirs
Apache, Alibaba databases vulnerable and only one has a patch

See through local AI lies with Irish eyes
ICCL Enforce project offers Verity fact-checking server

Dissatisfied: Three-fourths of AI customer service rollouts are a letdown
AI rollback rates hit 81% at firms with mature guardrails, suggesting enterprises are struggling to manage the systems in…
Mystery Microsoft bug leaker keeps the zero-days coming
Security pros warn YellowKey claim could make stolen laptops a much bigger problem
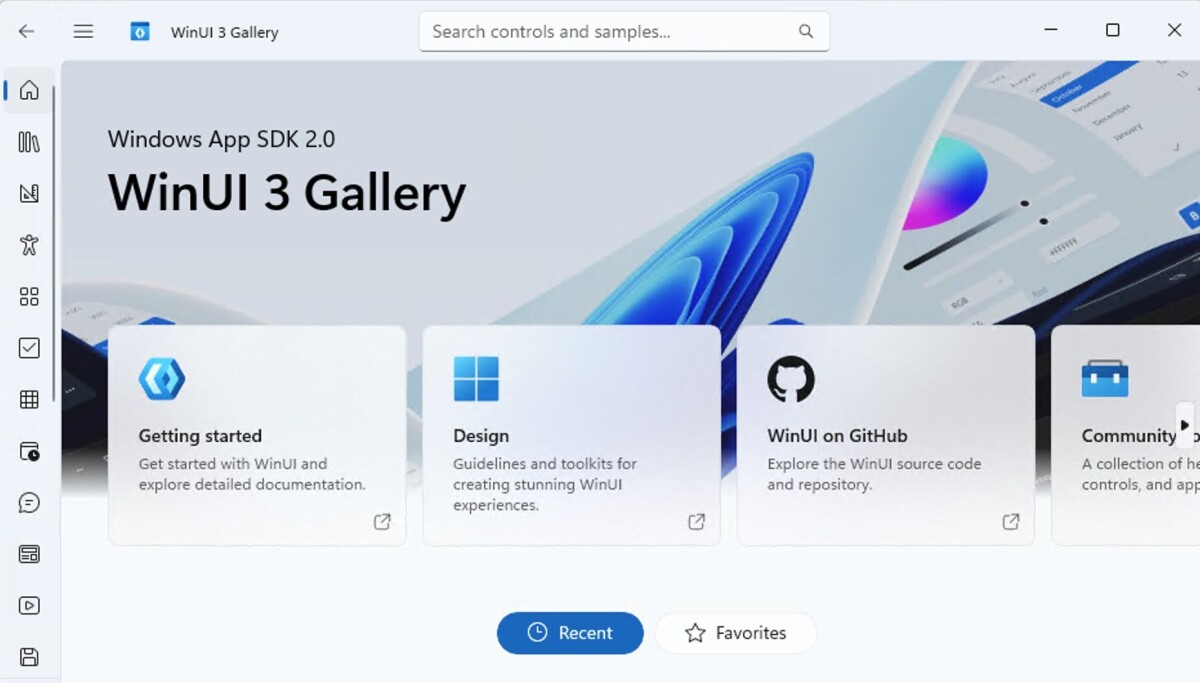
Microsoft aims to speed Windows with 'leap forward' in WinUI 3 perf
Bittersweet post tells devs what they already knew: The framework is too slow

Microsoft gives Windows Update a Ctrl-Z for bad drivers
Cloud-powered undo will roll back dodgy code without users or hardware partners lifting a finger

Linux gains more critical Windows apps: 3D Movie Maker and Space Cadet Pinball
Further demonstrating its role as industry default OS the versatility of modern porting tools

dBase debased: Database titan fades to black after 47 years
Blog post mourning decline appears to have helped knock what was left of the veteran app's online presence offline


Malware crew TeamPCP open-sources its Shai-Hulud worm on GitHub
Where it’s been well and truly forked, seemingly without Microsoft’s code locker noticing


Execs admit AI makes them value human workers less
As suits say they're burning cash on brainboxes without seeing results

Doozy of a Patch Tuesday includes 30 critical Microsoft CVEs
The good news: no 0-days. The bad news: busy week ahead for Microsoft admins

Google users fight for refunds as unauthorized API usage bills soar
'What the hell is going on? It's just draining my money'

Foxconn confirms cyberattack after ransomware crew claims it stole confidential…
Affected factories back up and running, we're told

Hollywood A-listers back proposed standard that would pay them when AI uses…
RSL Media expands machine-readable licensing rules to cover AI use of identities and creative works

Congress investigates Canvas breach as company pays ransom
Instructure CEO Steve Daly's got some explaining to do

AirBit crypto Ponzi victims can now claim slice of $400M asset haul
After guilty pleas, prison terms, and seizures, the DOJ has opened the compensation process


NHS England confirms: Palantir staff can access patient data
Tech firm's employees can get an 'admin' role letting them into the National Data Integration Tenant... and its identifiable…

Cache-poisoning caper turns TanStack npm packages toxic
Six-minute supply chain blitz pushed 84 malicious versions with credential theft and disk-wiping code

EU browser choice rules send millions more users Firefox's way
Mozilla claims the Digital Markets Act delivered lasting bump, invites Britain to do similar
Apple, Google drag cross-platform texting into the encrypted age
After years of stopping dead at the green bubble border, iPhone and Android users can finally send E2EE messages without relying…

FleetWave outage takes another turn. Chevin confirms crooks accessed customer…
A month after bringing systems back online, SaaS vendor tells customers attackers potentially walked off with operational data,…


GitLab promises a different kind of layoff as biz pivots toward AI
Code hosting biz is trimming its global footprint and flattening its management layer
Quit VMware and you’ll emerge with more complex and less capable infrastructure
Analyst says modernizing applications is probably a better use of your time than hypervisor migration

Double Canvas breach acknowledged as ShinyHunters sets new pay-or-leak deadline
UPDATED: Sorry, kids, everything's back up so get to work on your new assignment - An essay on the ethics of paying ransoms,…

Rodent-obsessed developer creates Ratty to bring 3D graphics to the command line
Inspired by TempleOS, this terminal emulator is just about as bonkers

Cookie thieves caught stealing dev secrets via fake Claude Code installers
New IElevator2 COM interface? No problem


Debian 14 cracks down on unreproducible packages
Dull but important … so, a bit like Debian itself, really

Anthropic’s bug-hunting Mythos was greatest marketing stunt ever, says cURL…
After all that hype, AI scanner found one low-severity cURL flaw

Gtk2-NG, next generation of Gtk 2, comes back to life
Debian 14 plans to ax Gtk2 – and hard pruning stimulates fresh growth

BWH Hotels guests warned after reservation data checks out with cybercrooks
Customers urged to keep an eye out for phisherfolk

Feature freeze for Python 3.15 as first beta released
JIT compiler much improved, but no reinstatement for leaky incremental garbage collector

Google says criminals used AI-built zero-day in planned mass hack spree
GTIG says AI-powered hacking has moved well beyond phishing emails and chatbot tricks

Water company's leaky security earns near-£1M fine
Utility provider failed to detect Cl0p ransomware attack for nearly two years

Checkmarx tackles another TeamPCP intrusion as Jenkins plugin sabotaged
Cybercrooks ruin engineers' weekends with Saturday attack

Linux kernel maintainers pitch emergency killswitch after CopyFail and Dirty…
Instead of waiting for patch cycles, admins could simply shut down vulnerable functions before attackers get there

Classic Outlook's Quick Steps trip over Microsoft bug
Client's handy automations get grayed out unless you know the keyboard shortcut

Taiwan's train cyber-trauma reveals a global system that’s coming off the tracks
That’s not a radio. THIS is a radio

Memory godboxes could offer relief from the RAMpocalypse
Amid the AI-fueled memory crunch, will Compute Express Link finally have its moment to shine?